Response to "Breaking web applications built on top of encrypted data" (CCS 2016)
by P. Grubbs, R. McPherson, M. Naveed, T. Ristenpart and V. Shmatikov.
Mylar provides end-to-end encryption for data fields a developer marks
with encrypted. In addition, Mylar provides two defenses against
active attacks: an attacker who controls the server cannot tamper
with the client software in a way that the client does not detect,
and the attacker cannot serve incorrect keys to clients during key
distribution. For fields marked as searchable (which allow search
on the encrypted data at the server), Mylar provides a different security
guarantee, which is common among existing searchable encryption schemes.
The Mylar paper elaborates on these guarantees
in the section "Security guarantees", explaining concretely what Mylar
gives and what it does not give.
A paper by Grubbs et al. (2016) considers three attack scenarios against Mylar:
two of these are out of scope for Mylar (as Grubbs et al. acknowledge), and the
third is prevented by Mylar.
We elaborate on a separate page.
Disclaimer: Mylar's code is an experimental research prototype and not a
product. The released version is for a passive attacker (the active attacker version is not ready for release). We do not guarantee that the implementation faithfully implements the system design, and there might be bugs or incompletely implemented features, so please use the paper as a reference.
If you notice something is missing or buggy, please contribute and fix it! We are releasing the source code in the hope that the community will contribute to it and take it further.
Play with Mylar! Download it using
git, and then follow the instructions in README.md.
git clone -b public git://g.csail.mit.edu/mylar
Our initial software (above) is based on an old version of Meteor, and hasn't been updated to Meteor's latest release. Thomas Steinhauer has ported Mylar to recent Meteor releases, which you can obtain below. Note that we did not validate this version.
https://github.com/strikeout/mylar
For more information on Mylar, contact mylar AT mit DOT edu.
Mylar is an experimental research prototype and not a product.
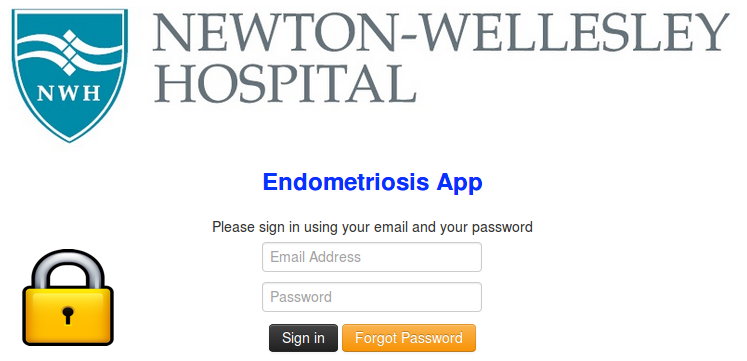
In our evaluation, we tested Mylar using existing applications including a medical application (performing
a survey of patients suffering from endometriosis) led by surgeons from Newton-Wellesley hospital. This medical application does not use
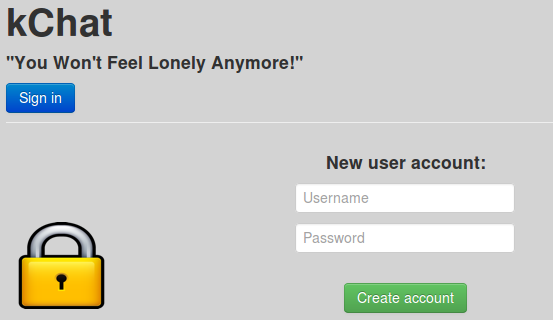
search, but uses the other features of Mylar. We also tested Mylar on an existing
chat application and on a class assignment submission website (for the MIT
class 6.858), as well as on experimental prototypes of a calendar, a forum application and a photo sharing application. We found that these applications can be ported to Mylar with minimal annotations and incurs a modest overhead.
Mylar's core has inspired some ideas in a startup PreVeil, but PreVeil aims at a different and simpler
problem space, where it
provides a more complete set of security properties than Mylar aimed at: it encrypts all the data at the server including metadata, it supports user access revocation, it protects against a broader range of active attacks, it provides user accountability, and does not use Mylar's search.